264.68.111.161: What This IP Address Means and Why It Matters
If you have come across 264.68.111.161 in your server logs, analytics reports, or firewall alerts, you may be wondering what it represents and whether it requires action. IP addresses are the foundation of internet communication, but not every address you see is automatically valid or trustworthy. Understanding how to interpret 264.68.111.161 can help you make informed decisions about your website’s security and performance.
Understanding the Basics of IP Addresses
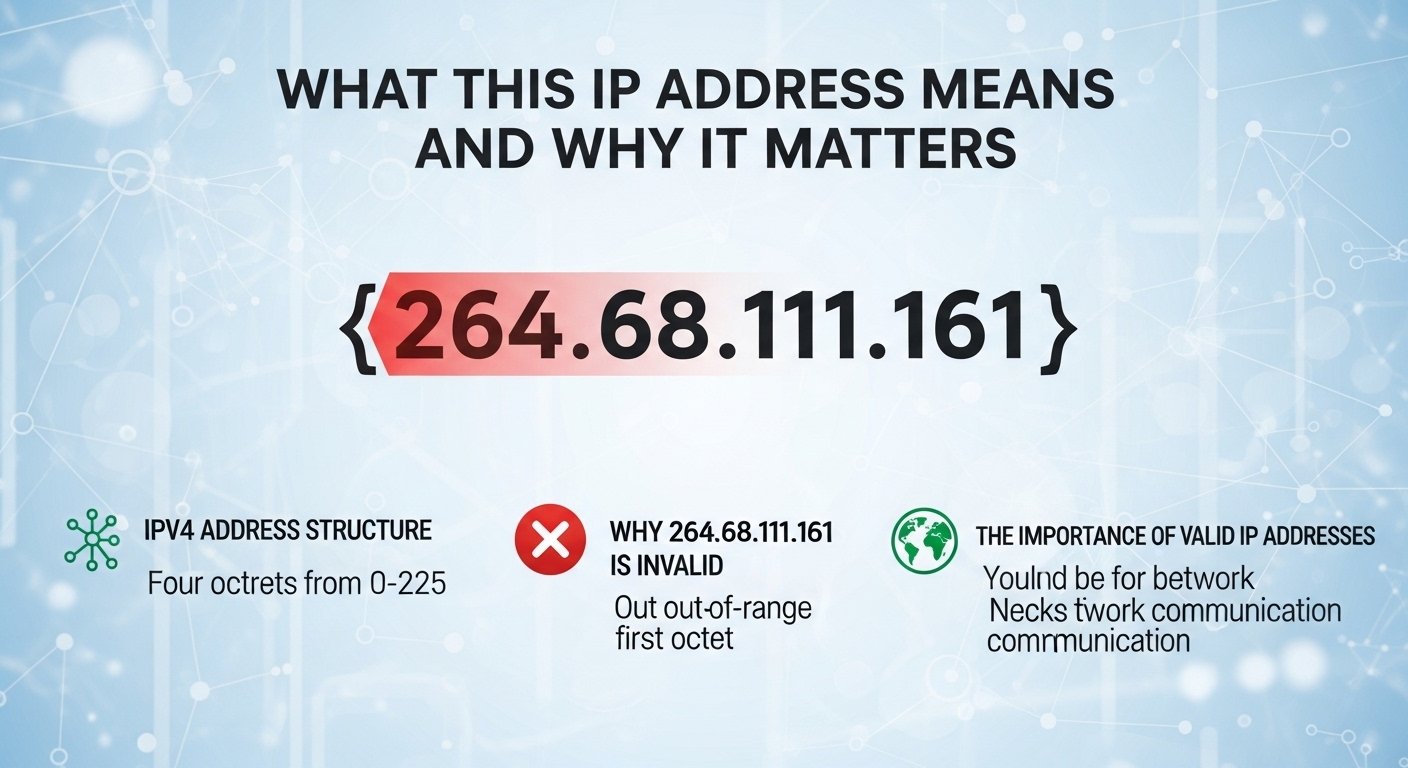
An IP address is a numerical label assigned to devices connected to a network. In IPv4 format, it consists of four numbers separated by dots. Each number must fall between 0 and 255. This structure allows routers and servers to direct traffic accurately across the internet.
At first glance, 264.68.111.161 appears to follow the standard IPv4 pattern. However, there is an important detail to notice: the first segment exceeds the allowed range of 0–255. That makes 264.68.111.161 technically invalid as a standard IPv4 address. This detail alone changes how it should be interpreted.
Why 264.68.111.161 Is Technically Invalid
IPv4 addresses cannot contain numbers higher than 255 in any segment. Since 264 is outside that range, 264.68.111.161 does not meet official formatting rules. This suggests several possibilities:
- A logging error in your system
- A spoofed IP address
- A placeholder used in testing
- Corrupted or malformed data in server headers
When 264.68.111.161 appears in logs, it is rarely a real public IP address. Instead, it often signals irregular traffic or data formatting issues.
How 264.68.111.161 Might Appear in Server Logs
There are several scenarios in which 264.68.111.161 could show up in monitoring tools.
1. Spoofed Request Headers
Attackers sometimes manipulate request headers to hide their real origin. In these cases, 264.68.111.161 may be inserted intentionally as a fake address. This tactic is common in automated scanning or probing attempts.
2. Misconfigured Proxy Chains
If your website sits behind a proxy or load balancer, incorrect header forwarding can produce malformed IP entries. 264.68.111.161 may result from a parsing issue rather than an actual device.
3. Data Corruption in Logs
Occasionally, server logs record corrupted entries due to encoding errors or software glitches. When this happens, values like 264.68.111.161 can appear even though no such valid IP exists.
Is 264.68.111.161 a Security Threat?
An invalid IP address such as 264.68.111.161 does not automatically indicate a security breach. The real question is not the address itself but the behavior associated with it.
If 264.68.111.161 appears alongside repeated login attempts, suspicious URL requests, or attempts to access restricted directories, it may signal malicious intent. On the other hand, if it shows up once in a harmless request for a public page, it may simply be a formatting anomaly.
The key is context. IP analysis should always include request patterns, timestamps, response codes, and user agent data.
Steps to Investigate 264.68.111.161 Properly
When you encounter 264.68.111.161, follow a structured review process instead of reacting immediately.
Review Access Logs Carefully
Check how many times 264.68.111.161 appears and what resources were requested. Look for patterns such as rapid consecutive requests or attempts to access administrative endpoints.
Inspect HTTP Headers
If you have access to raw headers, examine forwarded-for values and proxy headers. A malformed value like 264.68.111.161 may indicate header injection or spoofing.
Cross-Check with Firewall Logs
If your firewall flagged 264.68.111.161, review the reason. Was it rate limiting, suspicious payloads, or abnormal traffic volume? This helps determine whether the issue is genuine or technical noise.
Preventive Measures to Strengthen Security
Even if 264.68.111.161 turns out to be invalid or spoofed, it highlights the importance of strong security practices.
Enable Rate Limiting
Rate limiting prevents automated scripts from overwhelming your server. If malformed addresses like 264.68.111.161 appear frequently, rate controls reduce risk.
Use Web Application Firewalls
A properly configured firewall filters suspicious traffic before it reaches your application layer. This protects your system regardless of whether the IP is valid.
Keep Software Updated
Outdated CMS platforms, plugins, or server software create vulnerabilities. Keeping everything updated reduces exposure to automated scanning attempts that might generate entries like 264.68.111.161.
Monitor Logs Regularly
Consistent log monitoring allows you to detect irregular patterns early. If 264.68.111.161 appears repeatedly, you will notice trends before they escalate.
Understanding IP Spoofing in Depth
IP spoofing is a method where attackers forge the source IP address in network packets. Because 264.68.111.161 is invalid, it strongly suggests spoofing or malformed input. Attackers sometimes use unrealistic addresses to test how systems handle unexpected data.
Modern servers typically validate IP formats, but misconfigured applications may log spoofed values without verification. That is why reviewing 264.68.111.161 carefully is more important than dismissing it entirely.
When Should You Take Immediate Action?
You should respond quickly if:
- 264.68.111.161 appears in brute-force login attempts
- It repeatedly targets admin panels
- It triggers multiple firewall alerts
- It coincides with unusual server load spikes
In such cases, blocking suspicious traffic sources and tightening security controls is justified, even if the IP itself is technically invalid.
Conclusion
Seeing 264.68.111.161 in your logs may seem alarming at first, but understanding its structure provides clarity. Because the first segment exceeds IPv4 limits, 264.68.111.161 is not a valid public IP address. Its appearance often indicates spoofing, logging errors, or malformed header data rather than a direct threat.
Instead of focusing solely on the number, analyze the associated behavior. Look at request patterns, timestamps, and targeted resources. Strengthen your firewall, enable monitoring tools, and maintain updated software to reduce risk overall.
Ultimately, entries like 264.68.111.161 serve as reminders that cybersecurity is not about reacting to isolated data points. It is about observing patterns, applying best practices, and maintaining consistent vigilance.
Meta Description: